The Digital Transformation: Advanced Security course coverage of digital transformation and cybersecurity and blockchain fundamentals is further advanced with more in-depth explorations of blockchain architecture and application design, as well as cybersecurity mechanisms, processes and digital security solution components.
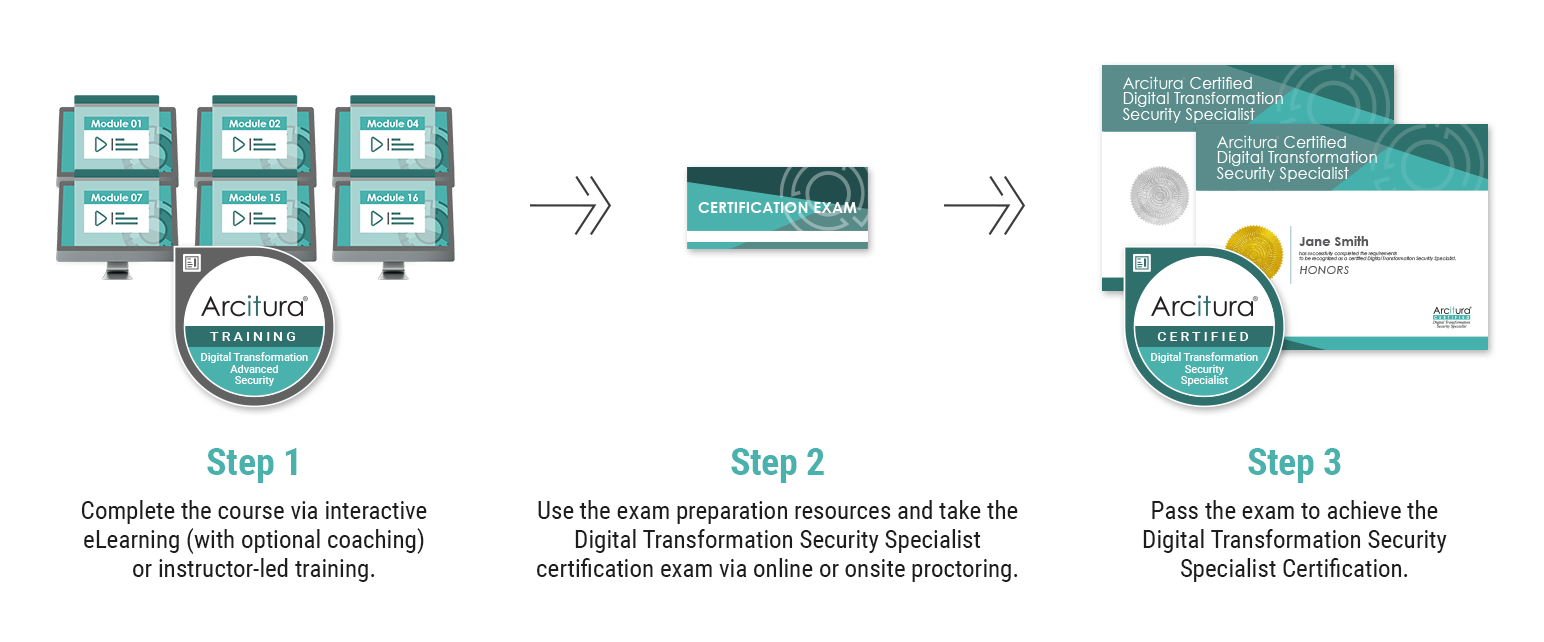
Complete the Digital Transformation: Advanced Security course and, optionally, get accredited as a Certified Digital Transformation Security Specialist by passing the certification exam. You can purchase the course now and get the exam later, or you can get them together at a discount as part of the Certification Bundle.
Upon completing the course you will receive a digital certificate of completion, as well as a digital training badge from Acclaim/Credly. Because this course encompasses multiple certifications, upon passing the exam you will also receive official Digital Transformation Specialist, Digital Transformation Security Professional and Digital Transformation Security Specialist digital accreditation certificates and certification badges from Acclaim/Credly, along with an account that can be used to verify your certification status.
If you already completed Modules 1, 2, 4 and 15 in this certification track, you can purchase a partial course (or a partial bundle) with only the modules specific to the Digital Transformation Security Specialist track here.
Choose the Certification Bundle to receive the entire course together with the online-proctored certification exam and a set of practice exam questions, all at a bundle discount.

Exam Details

Exam Details
Upon purchasing this course, you will automatically receive access via the Online Interactive eLearning platform. To provide you with the greatest flexibility, you will also have the option to access the course materials via two additional eLearning formats, at no extra cost. All three eLearning formats are briefly described below. A more detailed comparison can be found here.
- For everyday learning: An online interactive eLearning platform with individual lessons, as well as interactive and automatically graded exercises and practice questions.
- For learning on-the-go: A study kit platform with access to full course documents that support online/offline synching, annotations, comments, custom bookmarks and cross-document searches.
- For your reference: A set of printable watermarked PDF documents that you can keep (for all course workbooks and posters).
All three forms of access are subject to Arcitura’s *.
Upon purchase, access to the online interactive eLearning platform (1) is provided within one business day. Access to the study kits (2) and the PDF documents (3) is provided upon request.
The course is comprised of a set of modules. Each module has a set of lessons and is further supplemented with exercises to help reinforce your understanding of key topics. Shown below are the digital contents and the topic outline for each course module:
Module 1: Fundamental Digital Transformation
This course module provides an easy-to-understand introduction to Digital Transformation and how it relates to business, technology, data and people. Coverage includes the benefits, risks and challenges of Digital Transformation, as well as its business and technology drivers.
Course Module Contents
Topics Covered
Module 2: Digital Transformation in Practice
This course module delves into Digital Transformation automation environments by exploring the key contemporary technologies used to build Digital Transformation Automation solutions, including AI, RPA, IoT, machine learning, blockchain, cloud computing and big data.
Course Module Contents
Topics Covered
Module 4: Fundamental Blockchain
This course module provides a clear, end-to-end understanding of how blockchain works. It breaks down blockchain technology and architecture in easy-to-understand concepts, terms and building blocks. Industry drivers and impacts of blockchain are explained, followed by plain English descriptions of each primary part of a blockchain system and step-by-step descriptions of how these parts work together.
Course Module Contents
Topics Covered
Module 7: Blockchain Architecture
This course module delves into blockchain technology architecture and the inner workings of blockchains by exploring a series of key design patterns, techniques and related architectural models, along with common technology mechanisms used to customize and optimize blockchain application designs in support of fulfilling business requirements.

Course Module Contents
Topics Covered
Module 15: Fundamental Cybersecurity
This course module covers essential topics for understanding and applying cybersecurity solutions and practices. The module begins by covering basic aspects of cybersecurity and then explains foundational parts of cybersecurity environments, such as frameworks, metrics and the relationship between cybersecurity and data science technology.

Course Module Contents
Topics Covered
Module 16: Advanced Cybersecurity
This course module delves into the building blocks of cybersecurity solution environments and further explores the range of cyber threats that cybersecurity solutions can be designed to protect organizations from. Topics include cybersecurity technology mechanisms that represent the common components that comprise cybersecurity solutions, formal processes and procedures used to establish sound practices that utilize the mechanisms, as well as common cyber threats and attacks and how they can be mitigated using the previously described mechanisms and processes.
Course Module Contents
Topics Covered
Learn About Arcitura: Take the Video Tour
Watch these helpful informational videos to learn about Arcitura programs, courses and certifications.
About Arcitura
About Arcitura Courses
About Arcitura Certifications
What’s in an Arcitura Course
Comprehensive
Coverage
Each course provides a comprehensive curriculum with 2-3 modules and 20-40 hours of training.
More Than Just
Video Lessons
In addition to standard video lessons, courses include full-color workbooks and reference posters for all
lessons.
Interactive & Graded
Challenges
Courses also include interactive and graded exercises, interactive and graded self-tests and other
supplements.

The Arcitura Difference

EACH COURSE
- is authored by a dedicated courseware development team
- has a self-test, accreditation exam and professional certification
- is available via two different eLearning platforms
ALL COURSES
- undergo a common development process
- are authored to be consistent in quality, structure and style
- share a common vocabulary and symbol notation
- are authored in collaboration with subject matter experts
Take Your Skills Anywhere
Because both courses and accreditations are vendor-neutral, they empower you with skills and credentials that you can take to wherever you need to go.

Lifetime Access Guarantee
Access to the eLearning platforms is dependent on third-party platform providers. As a result, Arcitura cannot make any guarantees or warranties regarding the behavior or availability of the platforms, nor can Arcitura guarantee a specific duration for which these platforms will remain available. When your course is set up on an eLearning platform, your access will have no expiration date and will be provided indefinitely. The PDF documents that can be made available for you to download are yours to keep forever.